Privacy Challenges in Internet's first decade
 |
 |
Privacy Guidelines for Semantic Web Developers: be afraid, but not very afraid
Semantic Web Bootcamp
11 January 2007
Daniel J. Weitzner
Decentralized Information Group
MIT Computer Science and Artificial Intelligence Laboratory
W3C Technology and Society Domain Lead
These slides: http://dig.csail.mit.edu/2007/Talks/0111-privacy-design-patterns/
 |
 |
 |
 |
| Decade | Privacy Challenge | Policy Response |
| 1960-70s | Mainframe: collection limits |
Collection Limits |
| 1980s | Internet and Personal Computers: secrecy and channel security |
Security fixes |
| 1990s | Web: user control |
User Control/Choice |
| 2000- | Semantic Web |
?? |
General view (amongst the 'digerati'): law has to catch up with new technology.
General question: how will laws catch up?
My question: How will the Web finally catch up with the 'real world'?: in everyday life, the vast major of 'policy' problems get worked out without recourse to legal system.
Design goal: instrument the Web to provide seamless social interactions which allow us to avoid legal system the way we do in the rest of life
Global perspective: In the shift from centralized to decentralized information systems we see a general trend:
ex ante policy enforcement barriers -> policy description with late binding of rules for accountability
| "The Internet is 'a unique and wholly new medium of worldwide human
communication.'" ACLU v. Reno, United States Supreme Court (June 1997)
"Filters are less restrictive than COPA. They impose selective restrictions on speech at the receiving end, not universal restrictions at the source." Ashcroft v. ACLU, 542 US 654 (2004). |
 |
Traditional Approach to Copyright
 |
 |
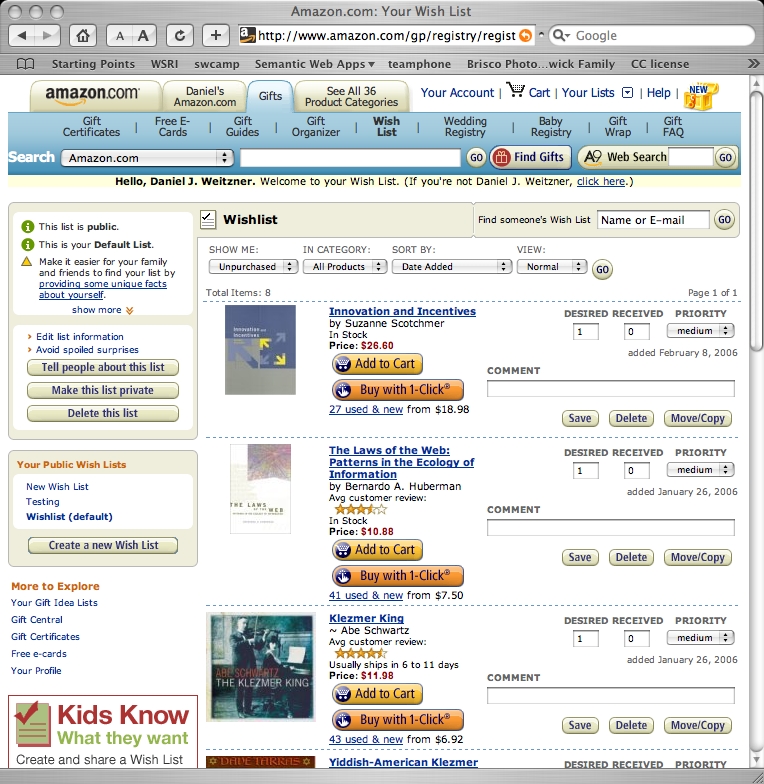
Departure from Hollywood content (centralized production) -> Blogs, Flickr and Livejournal (decentralized content we all make)
 |
 |
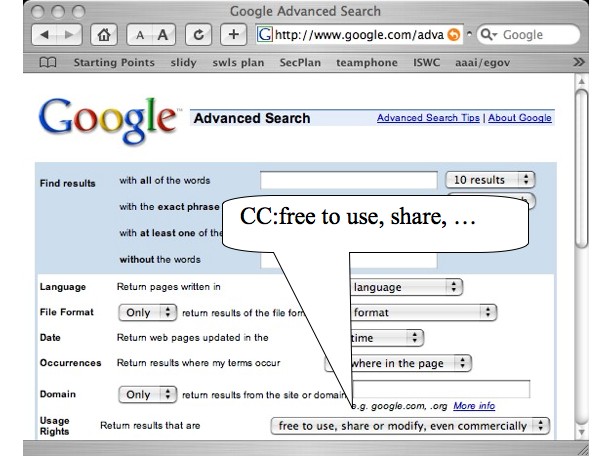
Move from up-front enforcement barriers (DRM) -> open description of licensing terms (CC) with after-the-fact enforcement as needed
Can today's model (EU or US) be sufficient going forward?
Key will be purpose limitation, but we have a dilemma...
Dilemma: limited individual and regulatory capacity to control escalating data collection.
Current result of consent dilemma + increased inference power: strict about what's collected but loose about usage
Better result: loose about what is collected and strict about usage
Why?
For more information see:
Work described here is supported by the US National Science Foundation Cybertrust Program (05-518) and ITR Program (04-012).
This work is licensed under a Creative Commons Attribution-NonCommercial-NoDerivs 2.5 License.